What is Cryptojacking and how can I prevent it?
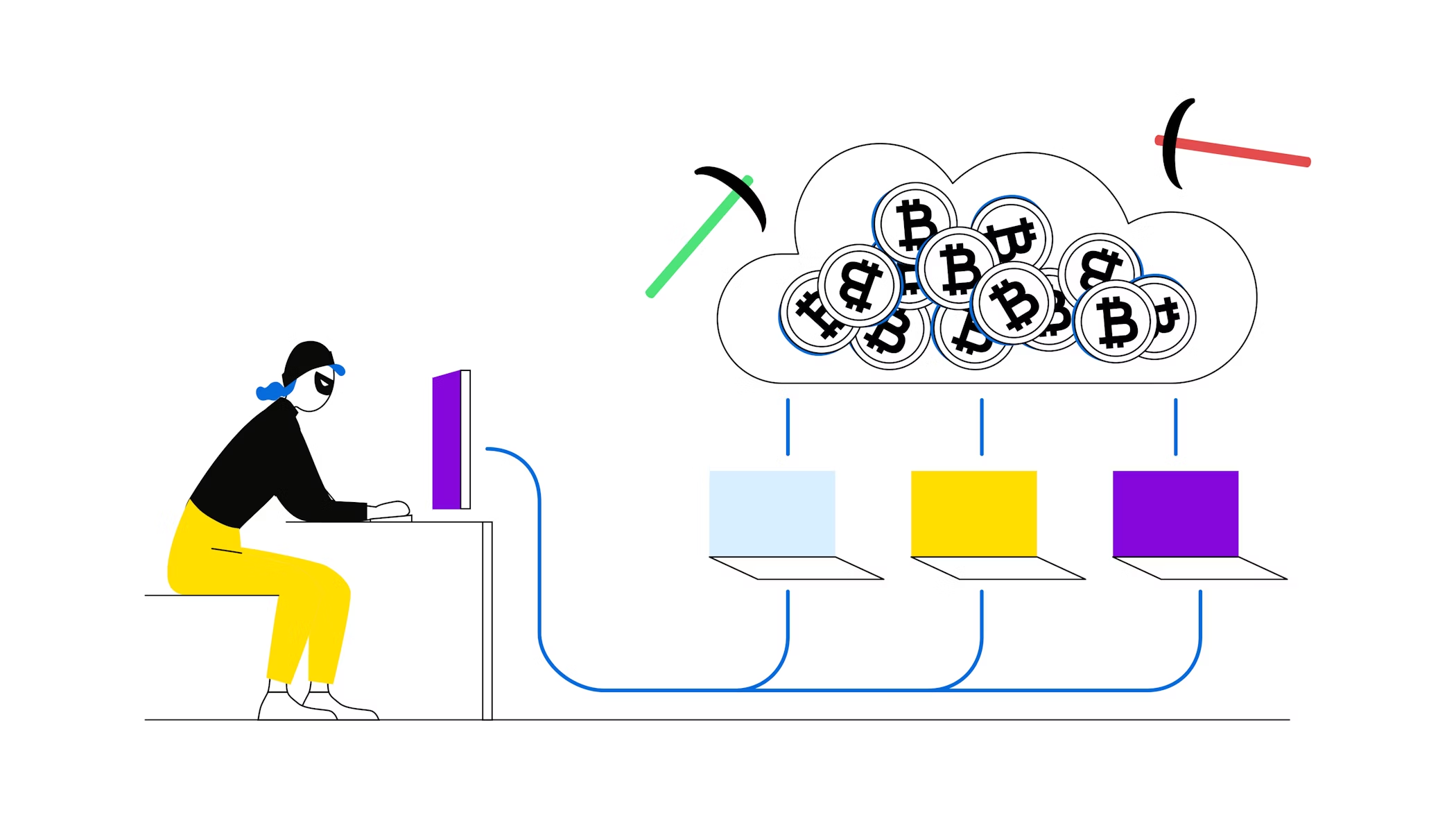
Cryptojackers use your computer or smartphone to mine a cryptocurrency using malware.
Cryptojackers mine cryptocurrency on your computer without you knowing
This can happen via your browser and without the need for any additional malware
There are easy ways to spot and prevent cryptojacking
In this article, you will learn about the danger of cryptojacking.
Watch this Bitpanda Academy lesson as video
Watch on YouTubeNew to Bitpanda? Get started today!
Sign up hereThe mining of Bitcoin and other cryptocurrencies is as energy and processing power consuming as it is lucrative. So it was just a matter of time until the shadier people online came up with ways to unknowingly abuse other users’ computers on the internet for their own financial gain. This practice is called cryptojacking - a fitting term to describe the combination of cryptocurrency and hijacking.
What happens while you are being cryptojacked is that your computer provides private processing power and energy to cryptojackers mining crypto without you even knowing it.
How does cryptojacking work?
Understanding cryptojacking is pretty simple: You visit a website and while you are there browsing the site, a malware script starts running in the background. This is usually just some basic lines of JavaScript code, which will then use your computer or smartphone to mine a cryptocurrency like the CPU-heavy, anonymity-focused Monero.
What happens while you are being cryptojacked is that your computer provides private processing power and energy to cryptojackers mining crypto with your resources without you even knowing it. There have also been reports of infected Chrome browser extensions, which have already been removed from the Chrome Web Store.
How can I protect myself against cryptojacking?
Browser-based cryptojacking is pretty easy to contend with, as you just need to install free browser extensions like minerBlock (Chrome) or No Coin (Chrome and Firefox) to stop it in its tracks.
Some people regard legitimate, voluntary mining of cryptocurrency in a browser as an alternative monetisation model, which could potentially replace ads on websites.
Is cryptocurrency mining in a browser always a bad thing?
No, it is not. In fact, some people regard legitimate, voluntary mining of cryptocurrency in a browser as an alternative monetisation model, which could potentially replace ads on websites.
For example, users could choose if they want to see ads or knowingly contribute a small portion of their processing power to mine a specific cryptocurrency as payment for avoiding ads. The same applies for charitable organisations, which could, for example, collect donations by asking visitors to install an application or stay on their website.
Are you ready to buy cryptocurrencies?
Get started nowThis article does not constitute investment advice, nor is it an offer or invitation to purchase any digital assets.
This article is for general purposes of information only and no representation or warranty, either expressed or implied, is made as to, and no reliance should be placed on, the fairness, accuracy, completeness or correctness of this article or opinions contained herein.
Some statements contained in this article may be of future expectations that are based on our current views and assumptions and involve uncertainties that could cause actual results, performance or events which differ from those statements.
None of the Bitpanda GmbH nor any of its affiliates, advisors or representatives shall have any liability whatsoever arising in connection with this article.
Please note that an investment in digital assets carries risks in addition to the opportunities described above.