What is a 51% attack and how is it prevented?
A “51% attack” occurs when a single miner or mining group takes majority control of a Proof of Work-based blockchain and double-spends some of its coins.
A 51% attack is quite possibly the problem most feared in the entire blockchain industry
In a 51% attack, one miner or mining group gains or purchases enough hash power to take control of 51% or more of a blockchain network and double-spend the cryptocurrency involved.
No successful 51% attack has been carried out on the Bitcoin blockchain so far, but it has happened in networks of altcoins with far less hashpower and poor network security
In this article, you are going to learn about the specifics of 51% attacks.
The GHash.IO incident
In June 2014, the mining pool GHash.IO reached a level of about 55% of Bitcoin’s hashrate over a 24-hour period. Up until this point, a 51% attack was purely hypothetical, especially in Bitcoin’s case, but suddenly, the threat of such an attack had become a reality. Even though a month later the share of GHash.IO in the network’s hashrate had fallen to just over 38%, the risk of one single miner or mining pool taking control once again remained. In this case, GHash.IO committed to keep itself down voluntarily.
In most cases, however, 51% attacks either fail or don’t succeed for very long. In fact, the GHash.IO incident, by definition, was not really a 51% attack since the mining group didn’t try to withhold blocks and/or double-spend on the network. However, since then, numerous actual 51% attacks have occurred on other smaller networks including Ethereum Classic. Thanks to its sheer volume and the agreement across the Bitcoin community to preserve the network at all costs, Bitcoin has remained secure to-date.
In most cases, however, 51% attacks either fail or don’t succeed for very long.
What happens during a 51% attack on a blockchain network?
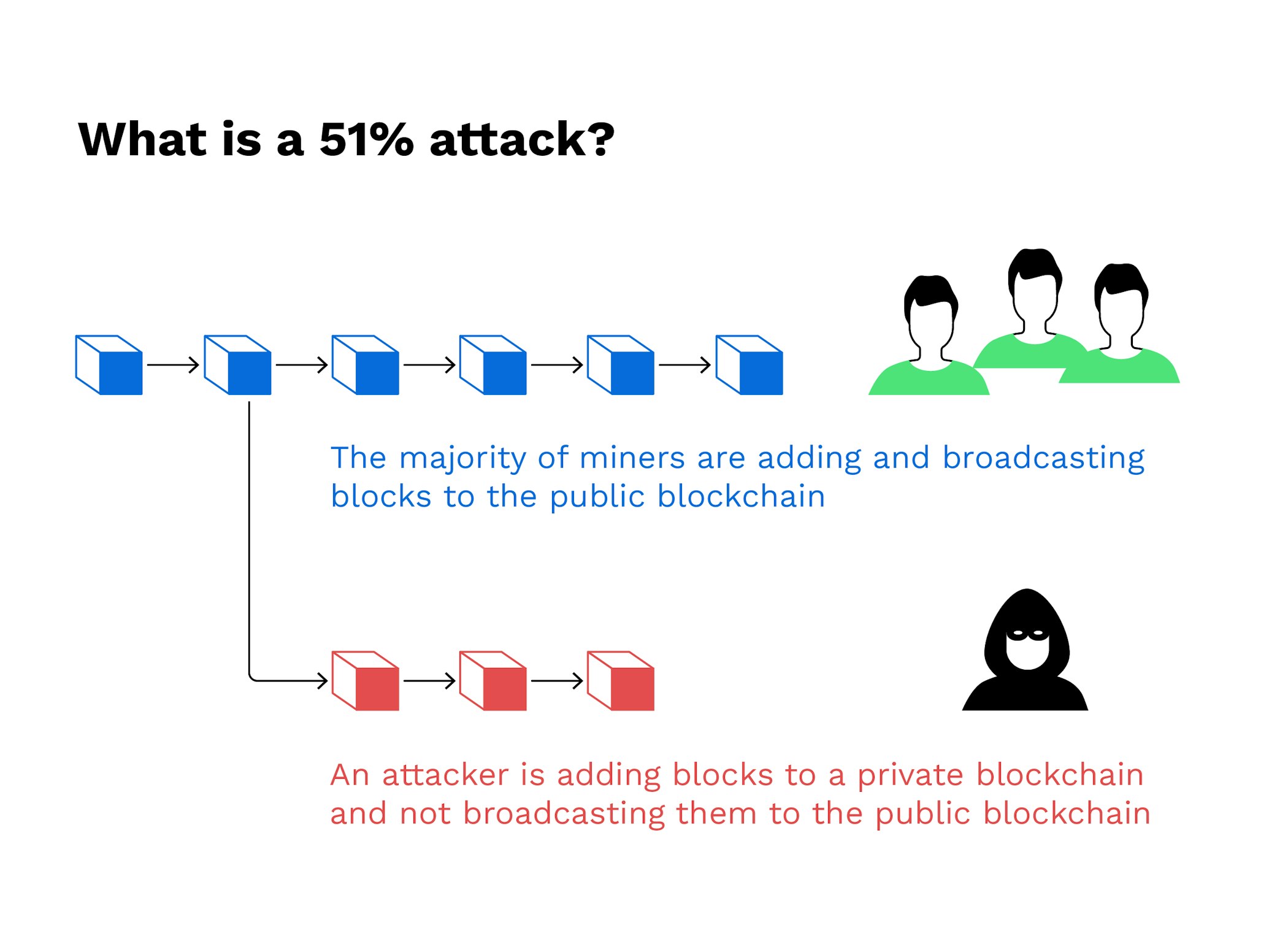
Under normal circumstances, new coins in the Bitcoin network are created by mining computers. Mining nodes are computers that compete against each other to uncover valid hashes by inputting different hashing combinations. Each node wants to be the first miner to find a new block. Once a miner finds a correct hashing combination, the newly mined block is then added to the blockchain and approved as legitimate by the network.
The agreement of nodes regarding what a legitimate block is based on is called consensus, meaning that the majority of nodes have to agree on the criteria that a new block is valid. If different miners find different valid blocks at the same time, the nodes trust the blockchain with the longest history and add the block there.
More than 50%
Hypothetically speaking, however, if one entity in the network does control more than 50% of the computational power, it could attempt to select the current block and then begin mining and withholding the mined blocks. When published, this competing chain will then overtake the original chain, leaving out all transactions since the fork and, consequently, sabotaging the network’s immutability. The perpetrating entity could also refuse to accept blocks mined by other network participants, ensuring the competition never receive a fair share, or even blacklist particular Bitcoin addresses.
An actual 51% attack happens in just a few steps. First, the entity or person that is interested in attacking the network would need to attain enough hash power to successfully mine blocks on a copy of the network’s chain in secret. This secret chain keeps going in parallel to the original. Therefore, the key to carrying out a 51% attack is buying a network’s hash power, hence this needs to be as costly as possible. If a malicious actor cannot pay to take over a network, then a 51% attack cannot occur.
On preventing 51% attacks
In his whitepaper, Satoshi Nakamoto outlined the nature of transaction fees in the Bitcoin network as an incentive for nodes to stay honest. By always ensuring that no single miner, group of miners or a mining pool is controlling more than 50% of the Bitcoin network’s computing power, a single miner or group wanting to attack the network will most likely not be able to outbuild the longest existing and validated blockchain. To do so, such a feat would require incredible amounts of hardware and energy. Also, the potential perpetrator would need a certain amount of luck on their side owing to the randomness of the mining process.
With Bitcoin, staging a 51% attack on the network is seemingly unlikely, simply due to the size of the network and its hash rate. One estimate puts the cost of running a 51% attack on Bitcoin at just over 15 billion USD. Many altcoins, however, are much more at risk. All it takes is sufficient rented mining equipment that doesn’t need to be kept in-house and a relatively large initial investment. It was for these factors Ethereum Classic was hacked and hackers stole the equivalent of more than 1 million USD of its native cryptocurrency. The overall network hash rate just doesn’t match up to Bitcoin’s.
The case for Proof of Stake
Nevertheless, even for the smallest blockchain networks it remains crucial to make it as difficult as possible for one miner to become the majority player. All Proof of Work-based networks have a built-in incentive for miners to improve their equipment on an ongoing basis. If they don’t do so, they begin to fall behind everyone else in a network and don’t receive any block rewards.
In line with this, the risk of a 51% attack is one reason why some advocates believe that Proof of Stake (PoS) is a more secure consensus mechanism than Proof of Work. True enough, in its most basic form, PoS incentivises control by the richest users but in most cases, networks have moved beyond this structure to more decentralised alternatives like Delegated-Proof-of-Stake (DPoS).
New to Bitpanda? Register your account today!
Sign up hereA strong network community
To quickly recap, DPoS allows any user who holds the network’s minimum level of stake to become a block validator - the equivalent to a miner in a Proof of Stake network. Typically, said validators are voted in by the community itself, as in the case of the cryptocurrency, EOS. Consider the fact that EOS is governed by 21 validators. If twelve or more of them even begin to collude to try to take control of the network, they can be quickly removed by the network’s community. This effectively prevents 51% attacks and therefore also prevents double-spending, since the rules for their removal are also coded into the blockchain, to an extent.
In the end, 51% attacks always remain a possibility. The key to preventing such heists is the community behind a network agreeing to uphold the value of immutability and to maintain decentralisation.
Are you ready to buy cryptocurrencies?
Get started nowThis article does not constitute investment advice, nor is it an offer or invitation to purchase any digital assets.
This article is for general purposes of information only and no representation or warranty, either expressed or implied, is made as to, and no reliance should be placed on, the fairness, accuracy, completeness or correctness of this article or opinions contained herein.
Some statements contained in this article may be of future expectations that are based on our current views and assumptions and involve uncertainties that could cause actual results, performance or events which differ from those statements.
None of the Bitpanda GmbH nor any of its affiliates, advisors or representatives shall have any liability whatsoever arising in connection with this article.
Please note that an investment in digital assets carries risks in addition to the opportunities described above.