Secure and compliant custody for digital assets
Built for institutions that demand the highest security and compliance.
Regulated custodial services across the UK, EU and MENA, complemented by global access through non-custodial solutions.
Certified security architecture
HSM-backed key custody with policy-based approvals and immutable audit logs.
Flexible deployment
Choose between Bitpanda Enterprise’s custodial or non-custodial models.
Regulated foundation
Operates under MiCAR, with FCA registration, VARA licensing and PSD2 alignment.
API-first design
Integrate custody workflows seamlessly into your systems.
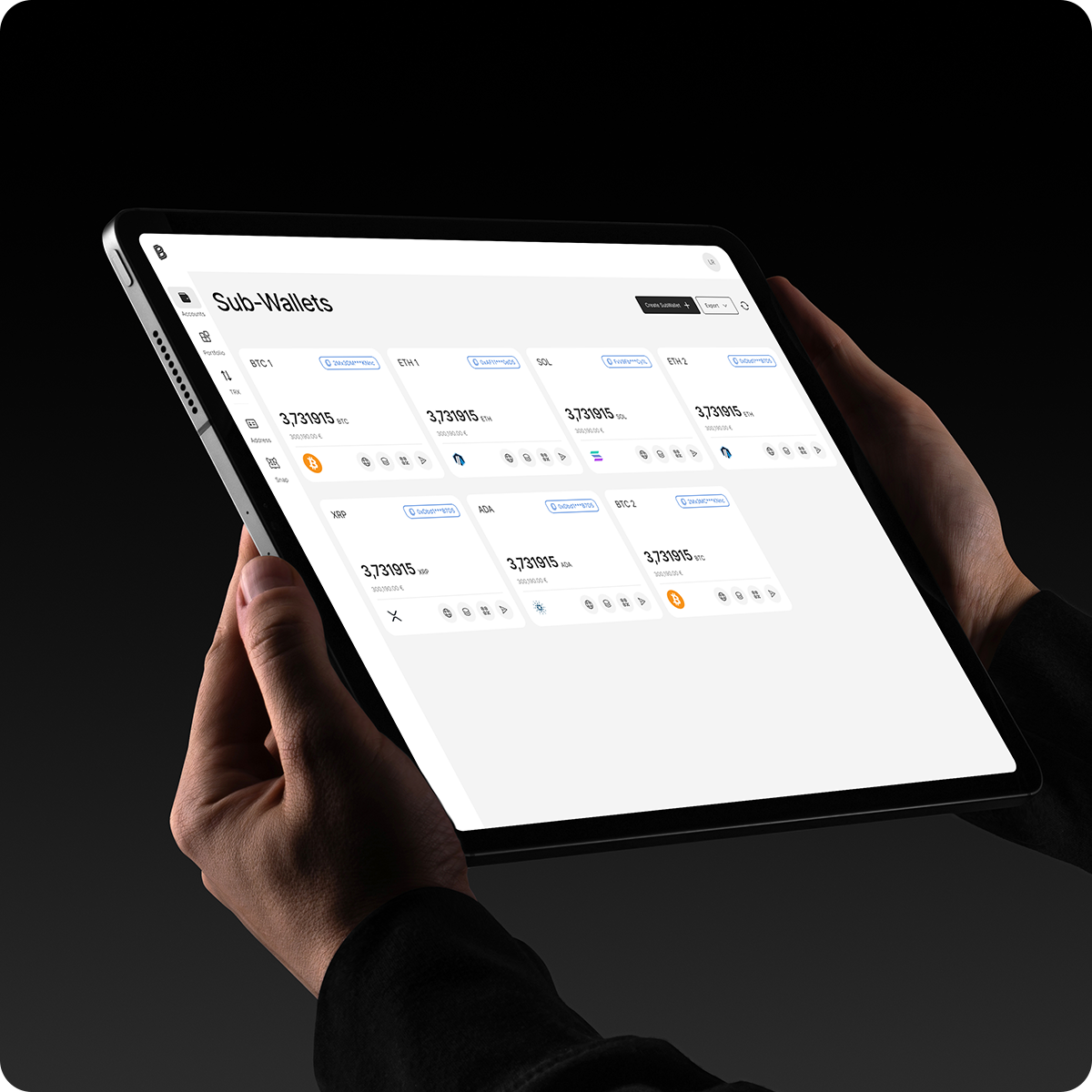
Assets & Networks
Support for BTC, ETH, major stablecoins and leading EVM L1/L2s, with a documented process to onboard additional networks on demand.
Choose your custody setup
Custodial (Bitpanda-managed)
Bitpanda operates the HSMs, signing workflows, and compliance. Choose between shared, logically segregated multi-tenant HSM cluster or a dedicated single-tenant HSM cluster that is physically and logically isolated.

Non-custodial (Partner-managed)
Operate the HSMs and take full responsibility. Run an online on-prem setup with real-time signing and quick approvals or an offline (air-gapped) on-prem setup for cold-storage-level security.